Archive
History Defines Our Present
Reflect, Learn, and Prepare
At RMS International, we understand the importance of historical context in shaping the present and preparing for the future. Our Archive subpage is a testament to this philosophy. It serves as an extensive repository of our past analyses and updates on global events, offering a relevant resource for those seeking to understand the evolution of security concerns over time.
What’s Covered
- Geopolitical Changes: Study previous geopolitical scenarios to prepare for future threats.
- Ecological Emergencies: Understand how past natural disasters have shaped global security dynamics.
- Cyber Security Landscapes: Explore the evolution of digital threats and cyber security.
- Public Health Developments: Track the trend of global health crises and their implications.
With RMS International, turn hindsight into foresight.
Blog
Visit the Archive

Small Circles, Big Consequences: Us, Them and the Space Between
For the vast majority of human history, Homo sapiens lived in small, tightly knit tribal groups, a structure that continues to shape modern social behavior, even in digital spaces. While this model fostered strong cohesion, shared purpose, and resilience, history demonstrates that when tribal identity hardens into exclusion, it can drive extreme violence, as seen in events like the Rwandan genocide and other modern ethnic conflicts. Today, although society has scaled beyond tribal life, the underlying instincts persist—manifesting in political polarization and identity-driven rhetoric—highlighting the enduring tension between our evolutionary wiring and the demands of modern civilization, and underscoring the need to manage, rather than eliminate, tribal dynamics.
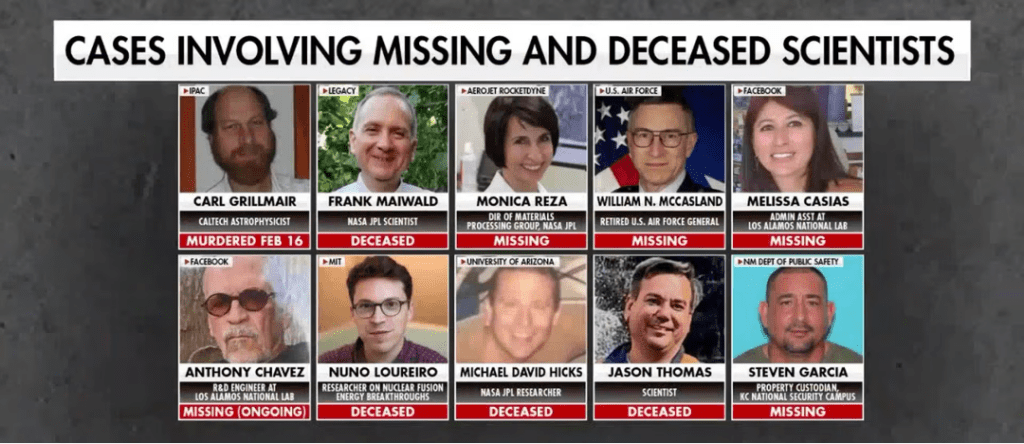
Missing Data: FBI Investigation into Cluster of Deaths and Disappearances Among US Scientists
US federal authorities, led by the FBI, are investigating a cluster of at least 10–11 deaths and disappearances involving scientists and officials with access to sensitive nuclear, aerospace, and defense-related programs.
Nothing Certain but Risk and Taxes
Tax filing, often perceived as a routine administrative task, has evolved into a concentrated point of modern risk, where sensitive personal data, digital systems, and time pressures converge. Today’s tax returns compile highly valuable identity information that moves across multiple platforms, increasing exposure to cyber threats such as phishing, account compromise, and data breaches. At the same time, compressed deadlines and the complexity of the tax code heighten the likelihood of human error, which can lead to financial loss, audits, or delays. While the process remains essential, it requires heightened vigilance, as seemingly minor lapses in attention or security can have outsized consequences in an increasingly interconnected and threat-prone environment.

Global Risk Forecast: Q2 2026 — The Season of Friction
Q2 2026 will be characterized not by a single defining crisis, but by the convergence of multiple, interdependent pressures across geopolitical, cyber, and environmental domains.
Seven Key Supply Chain Best Business Practices
Securing a modern supply chain requires a comprehensive, integrated approach that combines cybersecurity, physical security, and continuous risk management across both internal operations and third-party partners. Organizations must prioritize strong access controls, including role-based access and zero-trust principles, alongside effective log management to ensure accountability and rapid incident response. Continuous monitoring of systems, suppliers, and development pipelines, supported by real-time visibility technologies, enables early detection of threats and strengthens operational resilience. Equally critical is the inclusion of suppliers in security planning, incident response, and recovery efforts to ensure alignment and reduce systemic vulnerabilities. Regular penetration testing and vulnerability assessments further enhance security by identifying weaknesses across both software and infrastructure. Ultimately, supply chain security is an ongoing process that demands constant adaptation, collaboration, and proactive investment in resilience to mitigate evolving cyber and operational risks while maintaining business continuity.

RMS International April 2026 Look Ahead
April is defined less by singular flashpoints and more by persistent, overlapping activity cycles—religious, political, and civic—that collectively sustain an elevated baseline risk across U.S. urban centers, particularly downtown corridors, government zones, and large venue environments.
Forecasting Friction: When Predictions Meet Reality
As Q1 2026 concludes, early developments are aligning closely with RMS International’s Global Threat Forecast, reinforcing a security environment defined by converging geopolitical tensions, infrastructure fragility, and emerging technologies.
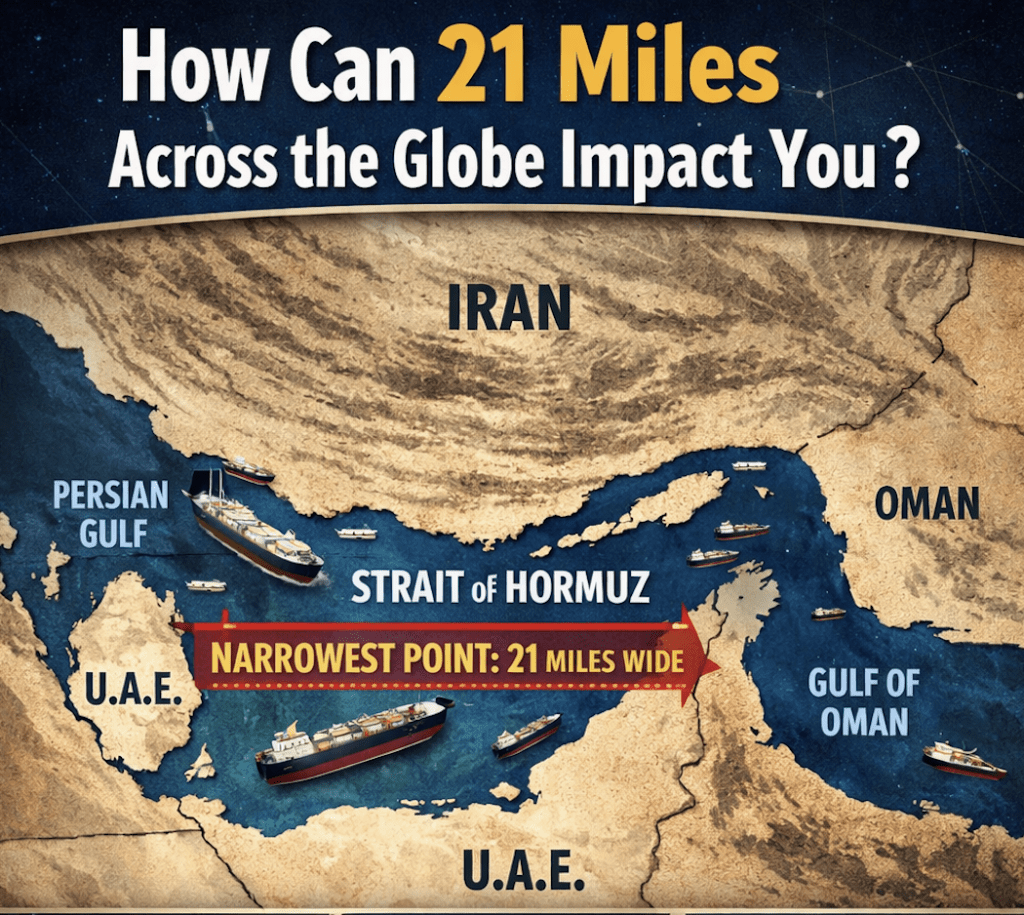
The Narrows of the Arabian Peninsula
The Strait of Oman becomes a growing 2026 flashpoint as Iran, Gulf states, and non-state actors are turning this vital maritime corridor into a zone of rising risk.
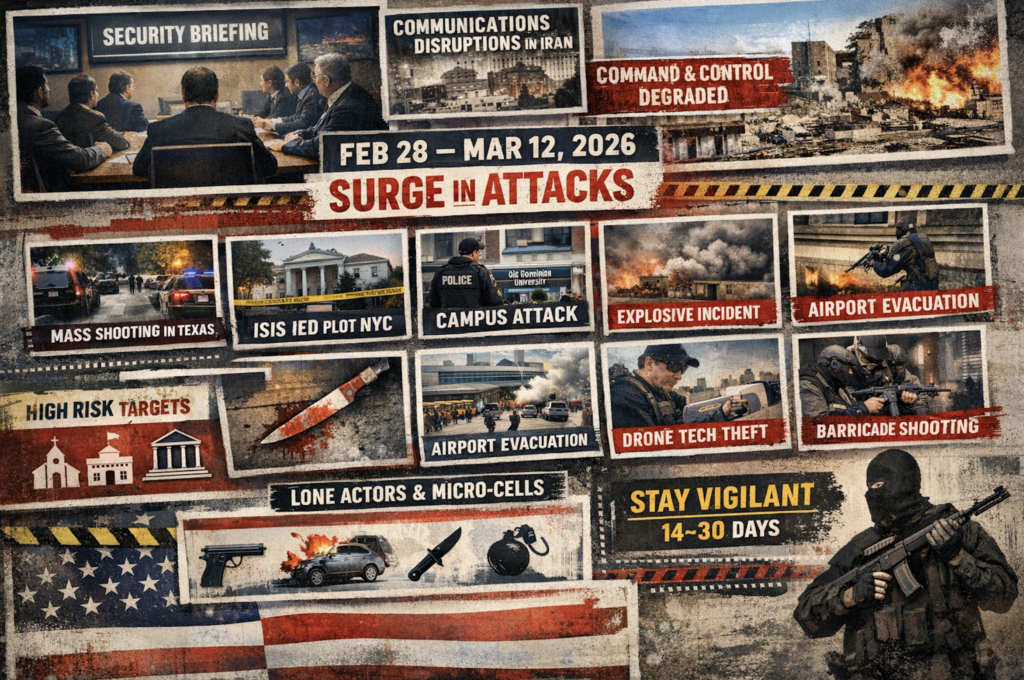
Epic Fury, Domestic Ripples
At a closed-door counterterrorism briefing, experts assessed that retaliation from Iran following Operation Epic Fury would likely be delayed due to communications disruptions, internet outages, and infrastructure damage inside Iran. Analysts initially believed the regime’s degraded command-and-control limited its ability to coordinate proxy attacks, potentially delaying retaliation against the United States (US) homeland by at least one month or longer. However, between 28 February and 17 March 2026, the US experienced at least nine security incidents involving lone actors or small cells.
