Situational Awareness
Staying One Step Ahead
Navigate the Present,
Prepare for the Future
In a world where threats can arise at any moment, situational awareness is not just beneficial, it’s critical. At RMS International, we leverage our globe-spanning expertise and technology to keep you informed and prepared. This section of our website is dedicated to providing you with up-to-the-minute insights and analyses of current global events, as well as a comprehensive archive for historical context.
Current Global Events
Stay abreast of the latest developments with our expert analyses. This real-time intel is designed to equip you with the knowledge needed to navigate today’s volatile security landscape.
Archive
Explore our extensive repository of past events for a clearer understanding of present threats and future possibilities. A valuable tool for those seeking to learn from history to shape better security strategies.
Blog
RMS International Archives
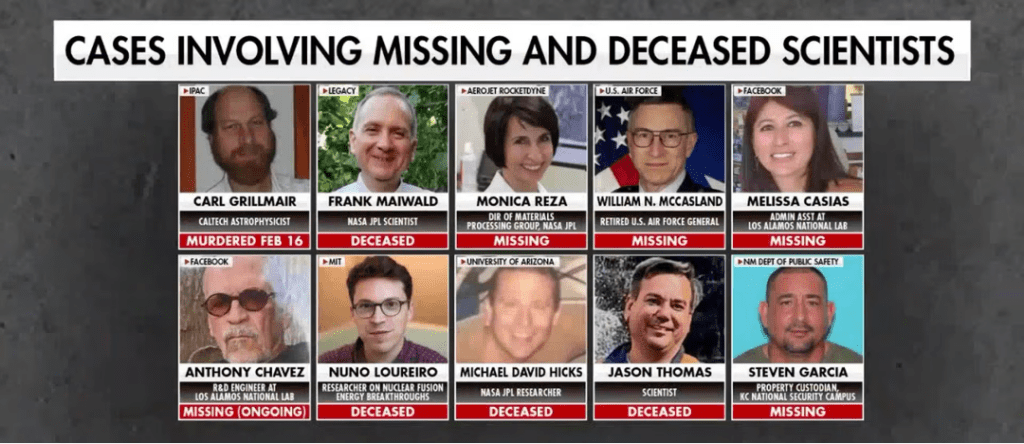
Missing Data: FBI Investigation into Cluster of Deaths and Disappearances Among US Scientists
US federal authorities, led by the FBI, are investigating a cluster of at least 10–11 deaths and disappearances involving scientists and officials with access to sensitive nuclear, aerospace, and defense-related programs.
Nothing Certain but Risk and Taxes
Tax filing, often perceived as a routine administrative task, has evolved into a concentrated point of modern risk, where sensitive personal data, digital systems, and time pressures converge. Today’s tax returns compile highly valuable identity information that moves across multiple platforms, increasing exposure to cyber threats such as phishing, account compromise, and data breaches. At the same time, compressed deadlines and the complexity of the tax code heighten the likelihood of human error, which can lead to financial loss, audits, or delays. While the process remains essential, it requires heightened vigilance, as seemingly minor lapses in attention or security can have outsized consequences in an increasingly interconnected and threat-prone environment.

Global Risk Forecast: Q2 2026 — The Season of Friction
Q2 2026 will be characterized not by a single defining crisis, but by the convergence of multiple, interdependent pressures across geopolitical, cyber, and environmental domains.
Seven Key Supply Chain Best Business Practices
Securing a modern supply chain requires a comprehensive, integrated approach that combines cybersecurity, physical security, and continuous risk management across both internal operations and third-party partners. Organizations must prioritize strong access controls, including role-based access and zero-trust principles, alongside effective log management to ensure accountability and rapid incident response. Continuous monitoring of systems, suppliers, and development pipelines, supported by real-time visibility technologies, enables early detection of threats and strengthens operational resilience. Equally critical is the inclusion of suppliers in security planning, incident response, and recovery efforts to ensure alignment and reduce systemic vulnerabilities. Regular penetration testing and vulnerability assessments further enhance security by identifying weaknesses across both software and infrastructure. Ultimately, supply chain security is an ongoing process that demands constant adaptation, collaboration, and proactive investment in resilience to mitigate evolving cyber and operational risks while maintaining business continuity.

RMS International April 2026 Look Ahead
April is defined less by singular flashpoints and more by persistent, overlapping activity cycles—religious, political, and civic—that collectively sustain an elevated baseline risk across U.S. urban centers, particularly downtown corridors, government zones, and large venue environments.
Forecasting Friction: When Predictions Meet Reality
As Q1 2026 concludes, early developments are aligning closely with RMS International’s Global Threat Forecast, reinforcing a security environment defined by converging geopolitical tensions, infrastructure fragility, and emerging technologies.
