Global Risk Forecast: Q2 2026 — The Season of Friction

Q2 2026 will be characterized not by a single defining crisis, but by the convergence of multiple, interdependent pressures across geopolitical, cyber, and environmental domains.
Seven Key Supply Chain Best Business Practices
Securing a modern supply chain requires a comprehensive, integrated approach that combines cybersecurity, physical security, and continuous risk management across both internal operations and third-party partners. Organizations must prioritize strong access controls, including role-based access and zero-trust principles, alongside effective log management to ensure accountability and rapid incident response. Continuous monitoring of systems, suppliers, and development pipelines, supported by real-time visibility technologies, enables early detection of threats and strengthens operational resilience. Equally critical is the inclusion of suppliers in security planning, incident response, and recovery efforts to ensure alignment and reduce systemic vulnerabilities. Regular penetration testing and vulnerability assessments further enhance security by identifying weaknesses across both software and infrastructure. Ultimately, supply chain security is an ongoing process that demands constant adaptation, collaboration, and proactive investment in resilience to mitigate evolving cyber and operational risks while maintaining business continuity.
Forecasting Friction: When Predictions Meet Reality
As Q1 2026 concludes, early developments are aligning closely with RMS International’s Global Threat Forecast, reinforcing a security environment defined by converging geopolitical tensions, infrastructure fragility, and emerging technologies.
The Narrows of the Arabian Peninsula
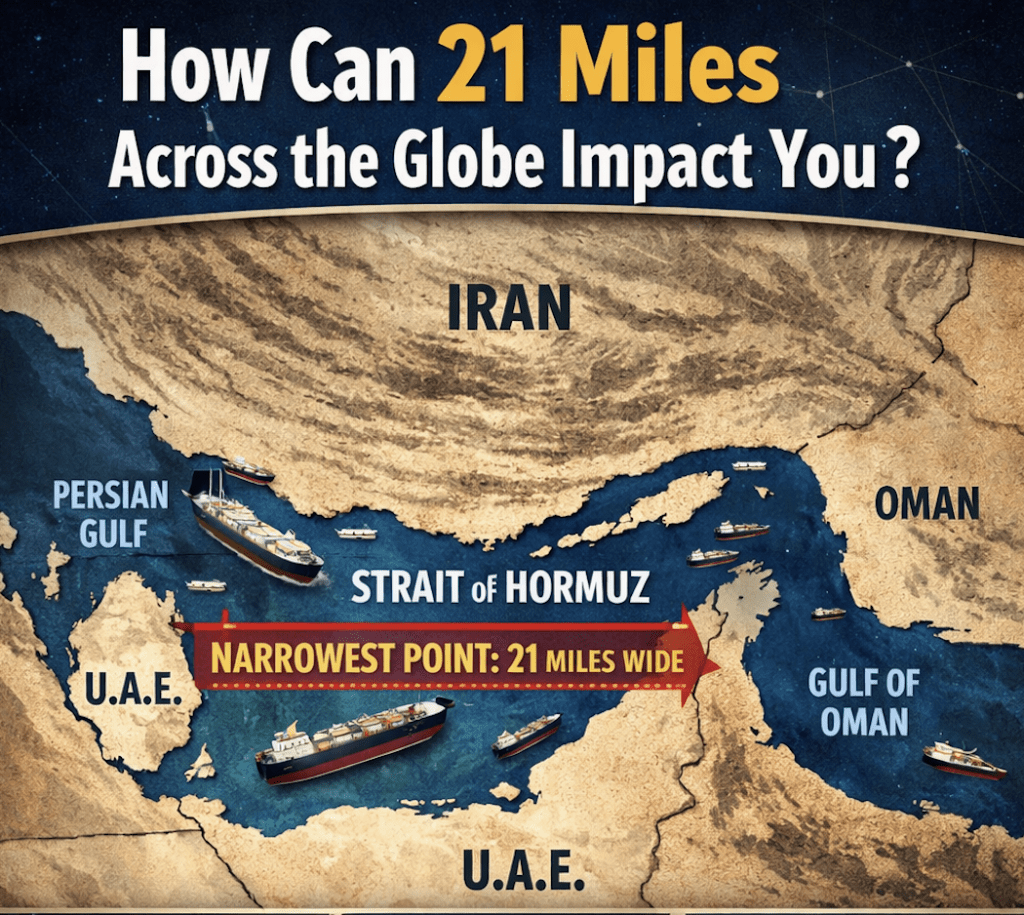
The Strait of Oman becomes a growing 2026 flashpoint as Iran, Gulf states, and non-state actors are turning this vital maritime corridor into a zone of rising risk.
Epic Fury, Domestic Ripples
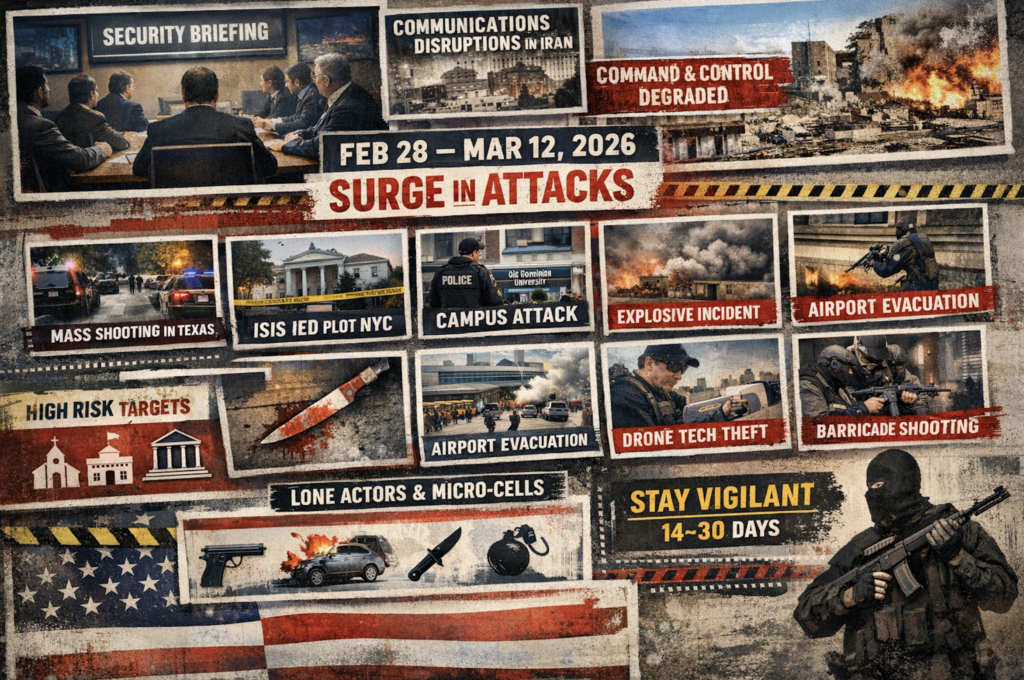
At a closed-door counterterrorism briefing, experts assessed that retaliation from Iran following Operation Epic Fury would likely be delayed due to communications disruptions, internet outages, and infrastructure damage inside Iran. Analysts initially believed the regime’s degraded command-and-control limited its ability to coordinate proxy attacks, potentially delaying retaliation against the United States (US) homeland by at least one month or longer. However, between 28 February and 17 March 2026, the US experienced at least nine security incidents involving lone actors or small cells.
Persian Pressure: Tehran’s Options for Payback
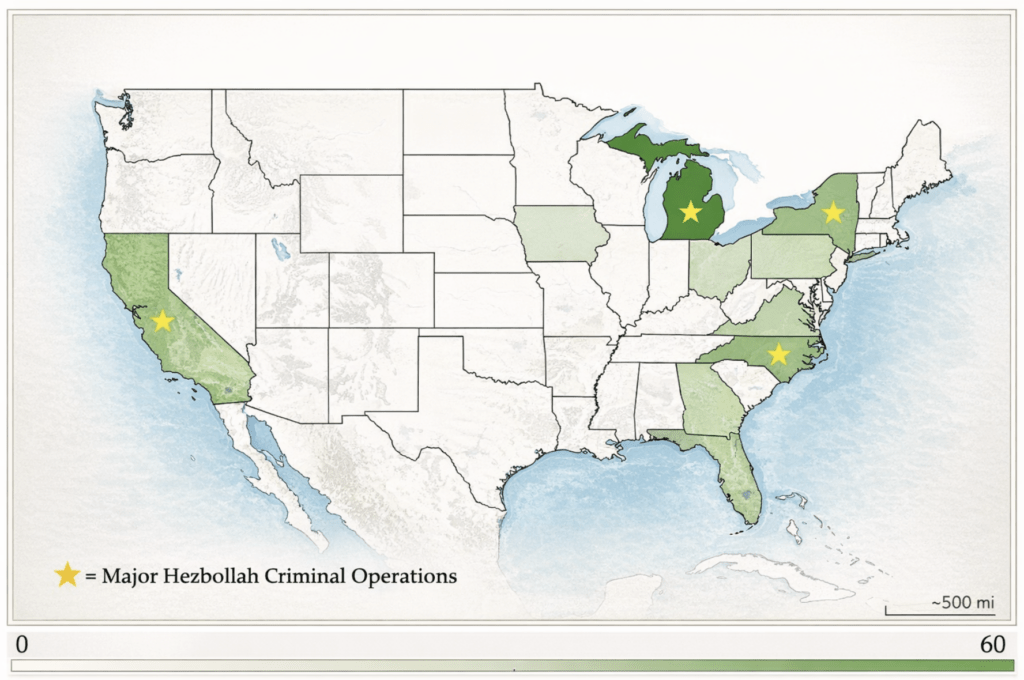
Iran rarely declares war. It retaliates in the shadows—proxies, cyber strikes, and deniable attacks that remind the homeland it isn’t beyond reach. Don’t expect Iran’s retaliation to look like war. Expect proxies, hacks, intimidation, and strikes designed to haunt the homeland.
Securing the Links: A Guide to Supply Chain Security

Supply chain vulnerabilities—digital or physical—represent a critical enterprise risk capable of cascading into full operational disruption. Effective supply chain security is a continuous intelligence-driven cycle of monitoring, validation, and enforcement. Organizations that adopt a secure-by-design posture are significantly better positioned to prevent disruption, detect threats early, and maintain operational continuity in a volatile global environment.
March 2026 Look Ahead

March 2026 presents a dynamic and event-driven risk environment shaped by the US election cycle, global protest activity tied to Middle East conflict spillover, religious observances, seasonal travel surges, and labor activism. Risk levels fluctuate throughout the month, with several identifiable high-impact dates requiring enhanced monitoring and protective posture adjustments. Additionally, The US Department of Homeland Security has warned of potential lone-actor and cyberattacks amid the ongoing strikes in Iran.
February 2026 Look Ahead

February 2026 presents a compressed risk environment driven by a convergence of major holidays, mass-gathering events, religious observances, and planned political demonstrations, particularly in Washington, DC. The highest-risk windows fall around Super Bowl Sunday (Feb 8), Mardi Gras/Lunar New Year (Feb 17), and late-month democracy-related mobilizations (Feb 21 and Feb 27–28). Organizations should anticipate crowd density, alcohol-related disorder, protest/counter-protest dynamics, transportation disruption, and heightened soft-target exposure.
Africa’s Two Roads Out of Beijing

China builds influence in Africa through massive infrastructure projects as the US pushes global de-risking—leaving Africa balancing both powers.
