Epic Fury, Domestic Ripples
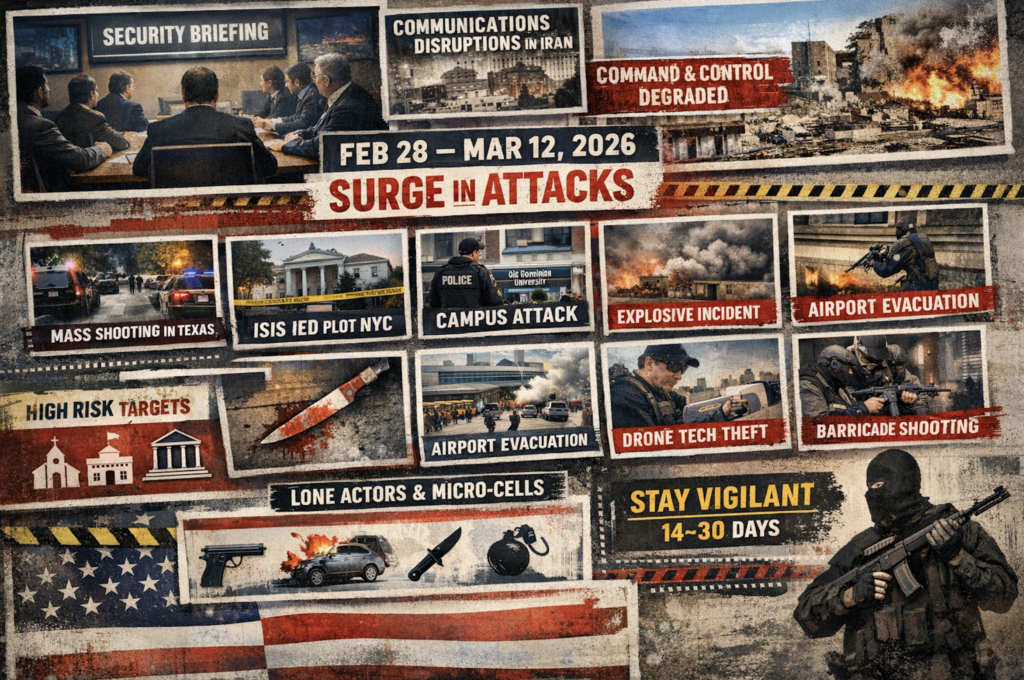
At a closed-door counterterrorism briefing, experts assessed that retaliation from Iran following Operation Epic Fury would likely be delayed due to communications disruptions, internet outages, and infrastructure damage inside Iran. Analysts initially believed the regime’s degraded command-and-control limited its ability to coordinate proxy attacks, potentially delaying retaliation against the United States (US) homeland by at least one month or longer. However, between 28 February and 17 March 2026, the US experienced at least nine security incidents involving lone actors or small cells.
Securing the Links: A Guide to Supply Chain Security

Supply chain vulnerabilities—digital or physical—represent a critical enterprise risk capable of cascading into full operational disruption. Effective supply chain security is a continuous intelligence-driven cycle of monitoring, validation, and enforcement. Organizations that adopt a secure-by-design posture are significantly better positioned to prevent disruption, detect threats early, and maintain operational continuity in a volatile global environment.
