Nothing Certain but Risk and Taxes
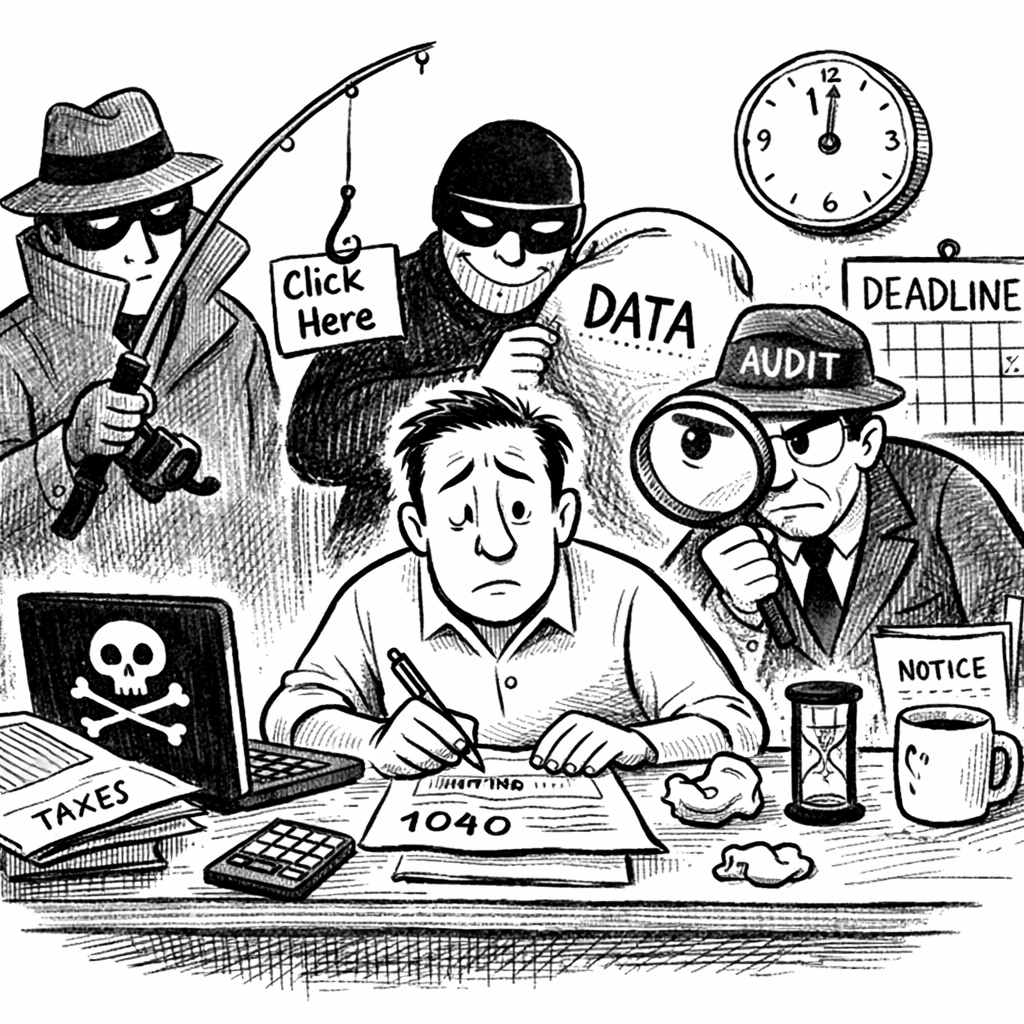
Tax filing, often perceived as a routine administrative task, has evolved into a concentrated point of modern risk, where sensitive personal data, digital systems, and time pressures converge. Today’s tax returns compile highly valuable identity information that moves across multiple platforms, increasing exposure to cyber threats such as phishing, account compromise, and data breaches. At the same time, compressed deadlines and the complexity of the tax code heighten the likelihood of human error, which can lead to financial loss, audits, or delays. While the process remains essential, it requires heightened vigilance, as seemingly minor lapses in attention or security can have outsized consequences in an increasingly interconnected and threat-prone environment.
Seven Key Supply Chain Best Business Practices
Securing a modern supply chain requires a comprehensive, integrated approach that combines cybersecurity, physical security, and continuous risk management across both internal operations and third-party partners. Organizations must prioritize strong access controls, including role-based access and zero-trust principles, alongside effective log management to ensure accountability and rapid incident response. Continuous monitoring of systems, suppliers, and development pipelines, supported by real-time visibility technologies, enables early detection of threats and strengthens operational resilience. Equally critical is the inclusion of suppliers in security planning, incident response, and recovery efforts to ensure alignment and reduce systemic vulnerabilities. Regular penetration testing and vulnerability assessments further enhance security by identifying weaknesses across both software and infrastructure. Ultimately, supply chain security is an ongoing process that demands constant adaptation, collaboration, and proactive investment in resilience to mitigate evolving cyber and operational risks while maintaining business continuity.
Persian Pressure: Tehran’s Options for Payback
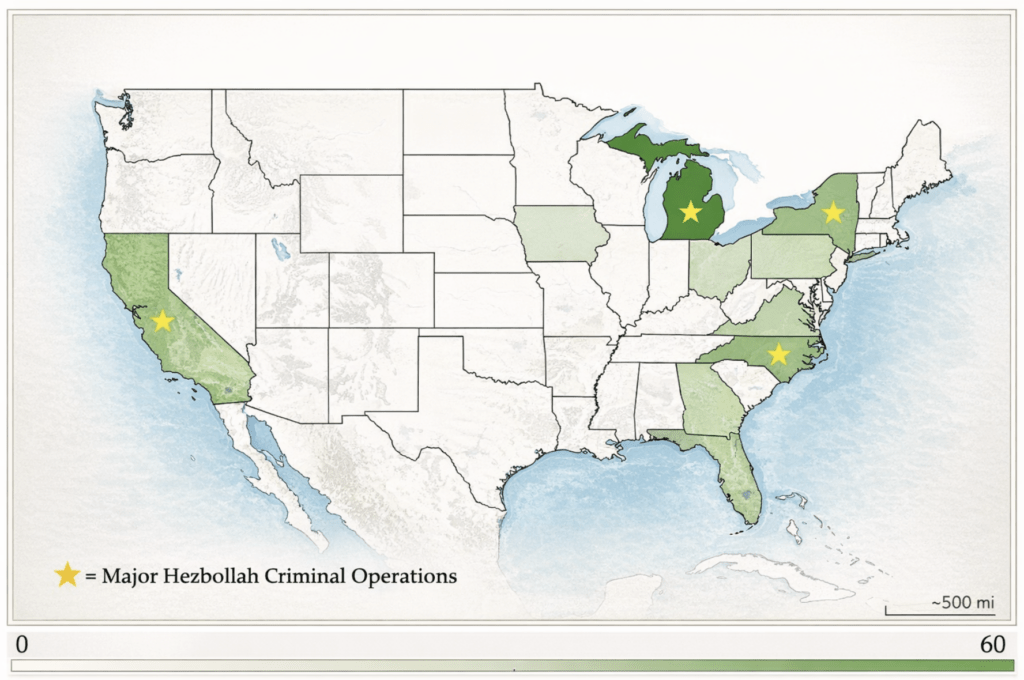
Iran rarely declares war. It retaliates in the shadows—proxies, cyber strikes, and deniable attacks that remind the homeland it isn’t beyond reach. Don’t expect Iran’s retaliation to look like war. Expect proxies, hacks, intimidation, and strikes designed to haunt the homeland.
Home Smart Home: The Surveillance State, Now Available in White or Stainless Steel

From doorbells to thermostats, our homes now observe us constantly—an intelligence network we installed ourselves.
Securing the Links: A Guide to Supply Chain Security

Supply chain vulnerabilities—digital or physical—represent a critical enterprise risk capable of cascading into full operational disruption. Effective supply chain security is a continuous intelligence-driven cycle of monitoring, validation, and enforcement. Organizations that adopt a secure-by-design posture are significantly better positioned to prevent disruption, detect threats early, and maintain operational continuity in a volatile global environment.
North American Infrastructure: The New Front Line

US infrastructure faces growing hybrid threats—cyber and physical attacks eroding resilience, trust, and stability as America races to adapt.
Crypto Kidnappings: Why Your Digital Wealth Isn’t as Safe as You Think

As cryptocurrency increasingly becomes more mainstream, a new trend has emerged: violent kidnappings and attacks targeting people just for their crypto holdings. Over the last 18 months there have been 231 documented physical incidents — abductions, home invasions, and other coercive attacks — aimed at individuals known or believed to hold significant.
Friendly Fire: When Attacking Yourself is the Best Defense

Nefarious actors are using machine learning to create deepfake voices, synthetic audio creations that have the same vocal, intonation, and pacing structure as an individual you may know very well.
Sounds Like Trouble: The Deepfake Voice Dilemma

Nefarious actors are using machine learning to create deepfake voices, synthetic audio creations that have the same vocal, intonation, and pacing structure as an individual you may know very well.
Gone Phishing: How Hackers Hooked Millions

Large-scale gatherings, such as fireworks displays, concerts, and sporting events, have long been considered attractive targets for lone actors or extremist groups. Expect increased patrols, bag checks, and drone surveillance in major metro areas.
