Executive Summary
|
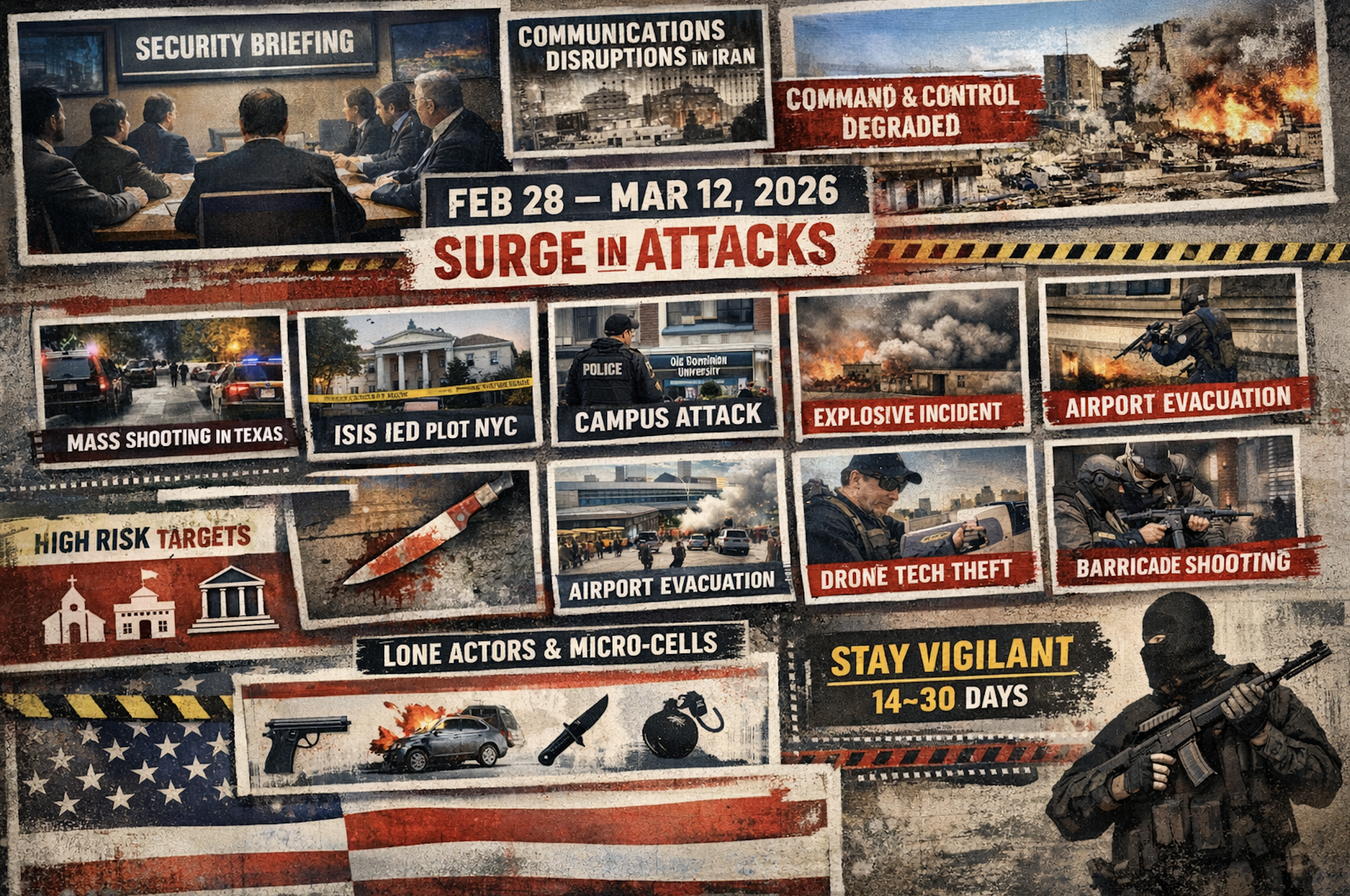
During a closed-door counterterrorism briefing, subject-matter experts assessed that Iranian retaliation for Operation Epic Fury would likely be delayed due to widespread infrastructure disruption inside Iran. Internet outages, blackouts, and degraded command-and-control capabilities were believed to be limiting the ability of remaining regime elements to communicate with regional proxies, temporarily delaying potential retaliation against United States (US) interests. Analysts initially assessed that attacks against the US homeland could occur one month or more after the operation, once Iran regained communication capabilities and operational coordination.
However, developments in the weeks immediately following the operation suggest that the retaliation window may have been underestimated. Between 28 February and 17 March 2026, the United States experienced at least nine notable incidents involving lone actors or micro-cells, including mass shootings, a confirmed ISIS-linked IED plot near Gracie Mansion, a terrorist campus shooting at Old Dominion University, and a vehicle-ramming and explosives incident targeting Temple Israel. Additional events included a knife attack on Interstate-495 in Virginia, a police barricade shooting in Baltimore, a public-safety evacuation at Kansas City International Airport, and an attempted theft of military drone technology near Colorado Springs, as well as four consecutive days of bomb threats prompting the Miami Zoo’s park closure.
While not all incidents appear ideologically motivated, the clustered timing and diversity of attack methods reflect a decentralized domestic threat environment dominated by lone actors and small cells employing low-complexity tactics, including firearms, knives, vehicles, and improvised explosive devices. Only a subset of events shows confirmed extremist links, but symbolic targets, such as government-adjacent locations, universities, and religious institutions are featured prominently, underscoring their continued appeal for attackers seeking high psychological and media impact.
The overall pattern does not indicate a coordinated campaign directed by a foreign state, but rather a permissive threat environment in which geopolitical tensions, extremist narratives, and opportunistic violence intersect. In such environments, even unrelated incidents can produce a cumulative operational effect by increasing public anxiety, straining law-enforcement resources, and elevating the risk of copycat attacks.
Since Operation Epic Fury began on February 28, 2026, there have been at least nine attacks involving mass shootings, campus shootings, vehicle ramming attacks, IED or bombing attempts, knife or stabbing attacks, attacks on religious institutions, attacks on government facilities, attacks on public gatherings, extremist or terrorism-related plots, airport closures and public safety responses, and theft or theft attempts of military or government grade technology or equipment:
Date | City/State | Method | Actors | Fatalities | Injured | Operational Notes |
01MAR26 | Austin, Texas | Mass Shooting | 1 | 3 | 15 | Attack occurred in crowded entertainment district; FBI reviewed possible geopolitical indicators but no confirmed ideological motive. |
02MAR25 | Fairfax, Virginia | Knife Attack | 1 | 1 | >2 | Escalated interpersonal violence after crash; suspect shot by state police. |
07MAR26 | New York, New York | IED Attack | 2 | 2 | 0 | Two suspects attempted to detonate improvised explosive devices during protests near Gracie Mansion. |
08MAR26 | Kansas City, Missouri | Public Safety Closure | Unknown | 0 | 0 | Terminal evacuation and flight delays at Kansas City International Airport after suspicious threat report; no credible device found. |
10MAR26 | Baltimore, Maryland | Armed barricade | 1 | 0 | 1 | Gunman fired on officers responding to burglary call; hostage-style standoff ended with suspect killed. |
12MAR26 | Norfolk, Virginia | Mass Shooting | 1 | 1 | 2 | Shooting inside business building at Old Dominion University; suspect previously convicted in ISIS-support case. |
11MAR26 | Colorado Springs, Colorado | Military Tech Theft | 2 | 0 | 0 | Suspects attempted to access and remove drones from a military storage facility. Both suspects arrested by military and federal authorities.
|
12MAR26 | West Bloomfield, Michigan | Vehicle, Firearm, possible IED | 1 | 0 | 1 | Attacker rammed vehicle into Temple Israel; explosives discovered in vehicle. |
13MAR26 – 16MAR26 | Miami, Florida | Bomb Threat | 0 | 0 | 0 | For four days in a row, the Miami Zoo has received bomb threats prompting park closures and law enforcement response. |
The strongest confirmed entries in this window are the Austin mass shooting, the Gracie Mansion ISIS-linked IED plot, the Old Dominion terrorist shooting, the Temple Israel attack, and the Kansas City airport evacuation as a major public-safety response rather than a confirmed attack.
Incident Distribution | |||||
Target Types | Attack Methods | Ideological Assessment | |||
Public gatherings | 1 | Firearms | 2 | Confirmed Extremist | 3 |
Transportation/Roadway | 1 | Knife | 1 | Possible Extremist Nexus | 1 |
Government-adjacent | 1 | IED/Explosives | 1 | Criminal/Grievance | 2 |
Airport/Infrastructure | 1 | Vehicle Ramming | 1 | Unknown/Unresolved | 1 |
Law Enforcement | 1 | Armed Barricade | 1 | ||
Education Institution | 1 | Security Threat Response | 1 | ||
Religious Institution | 1 | ||||
Confirmed extremist incident | Possible Extremist Nexus |
|
|
Intelligence Analysis and Recommended Course of Action
Between February 28 and March 17, 2026, the US saw a short but notable cluster of lone-actor and micro-cell incidents spanning mass shooting, attempted bombing, campus violence, an attack on a synagogue, and several high-visibility security responses. The most substantiated cases in that window include the 01 March Austin mass shooting, the 07 March Gracie Mansion ISIS-linked improvised explosive device (IED) plot, the 12 March Old Dominion University terrorist shooting, and the 12 March Temple Israel vehicle-ramming/armed attack in Michigan. DHS also warned in early March that, following the Iran strikes, large-scale attacks were unlikely but targeted attacks, lone-wolf violence, and cyber retaliation were credible concerns.
The pattern does not suggest a centrally directed campaign. It points instead to a decentralized domestic threat environment in which a mix of ideologically motivated actors, unstable grievance-driven individuals, and opportunistic violent offenders exploit a moment of heightened tension. The common thread is not command-and-control; it is permission structure. When geopolitical conflict dominates headlines, symbolic targets become more salient, online propaganda has more emotional fuel, and individuals already predisposed to violence may mobilize more quickly and with less planning.
From a targeting perspective, this window is notable because symbolic institutions that were selected. Gracie Mansion represented a government-adjacent political symbol, and Temple Israel represented a religious/community symbol during a period of elevated concern around Israel, Iran, and antisemitic violence. The Old Dominion University attack took place in the ROTC department, a military target. Those choices matter because symbolic targets generate outsized psychological effect even when casualty counts are low or the attack is disrupted. In intelligence terms, this is a reminder that attackers do not need high sophistication to produce strategic impact; they only need access, timing, and a target with narrative value.
Methodologically, the incidents reinforce that the dominant US threat remains low-complexity, mixed-method violence. Firearms remain central, but the Gracie Mansion case shows continued interest in IEDs, while the Michigan synagogue attack demonstrates the disruptive potential of vehicle ramming plus possible firearms/explosives. While Austin, Texas and Old Dominion employed active shooting tactics. These are attractive attack methods because they are comparatively accessible, difficult to predict with precision, and capable of bypassing organizations that prepare for only one mode of attack. The implication is that many security programs remain too stove piped: they plan for a shooter, or a protest, or a vehicle threat, instead of a blended event.
A second key judgment is that tempo matters as much as ideology. The clustering of terrorist inspired events does not prove coordination, but it does raise the perceived threat level, increases public anxiety, and taxes local response systems. In practical terms, that means organizations should not wait for proof of a network before hardening posture. In a fragmented threat environment, simultaneity without coordination can still create operational strain and reputational shock.
About RMS International
The world is unpredictable. Your security shouldn’t be. Founded in 2012, RMS International delivers discreet executive protection, intelligence, cyber security, and global travel risk management. From our Risk Operations Center in West Palm Beach, Florida, our analysts maintain continuous global overwatch—tracking emerging threats and safeguarding operations across five continents.
RMS International — peace of mind in a chaotic world.
#ThreatAssessment #ProtectiveIntelligence #SituationalAwareness #DomesticSecurity #NationalSecurity #Counterterrorism #PublicSafety #SecurityAnalysis #LoneActorThreat #MicroCellThreat #MassCasualtyThreat #SoftTargetRisk #CriticalInfrastructure #EventSecurity #ThreatEnvironment #Iran #MiddleEastConflict #Geopolitics #StrategicRisk #GlobalSecurity #SecurityProfessionals #RiskIntelligence #SecurityLeadership #IntelligenceAnalysis #SecurityOperations #ThreatAssessment #ProtectiveIntelligence #Counterterrorism #NationalSecurity #DomesticSecurity #SituationalAwareness #LoneActorThreat #SoftTargetRisk #SecurityAnalysis #StrategicRisk
